
NPM Package Registry Clone — Private Enterprise Software Distribution
Built a scalable, serverless package management system with automated quality scoring across 7 metrics, using AWS Lambda, S3, DynamoDB, and presigned-URL security.
Key Highlights
- •8 REST endpoints with complete package lifecycle management (upload, download, search, update, reset)
- •Automated quality scoring across 7 metrics: ramp-up time, responsiveness, correctness, bus factor, license compliance, dependency pinning, and code review fraction
- •Serverless architecture scaling within AWS free tier with minimal operational overhead
- •Presigned-URL security for time-limited (10-minute) S3 access, avoiding Lambda 6MB payload limits
Tech Stack
System Architecture
Key Features & Implementation Details

Website frontend
Development Process & Challenges
Security Analysis (STRIDE Model)

GitHub Actions CI/CD pipeline execution
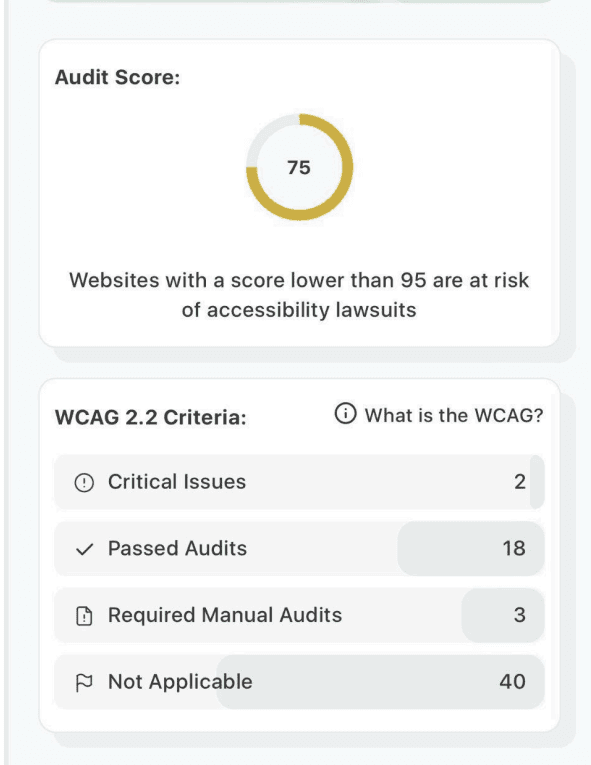
WCAG Accessibility Test
Outcomes & Lessons Learned
Overview
Build a scalable, secure, private package management system for enterprise use that evaluates and stores software packages with automated quality metrics, access controls, and a web-based interface—essentially creating a private alternative to the public npm registry. Designed and implemented a serverless architecture on AWS with 8 RESTful API endpoints supporting full CRUD operations for package management. Developed Lambda functions in TypeScript for package ingestion with automated quality scoring, upload/download via presigned S3 URLs, regex-based search, and cost calculation. Implemented comprehensive CI/CD pipeline using GitHub Actions for automated testing, security scanning (RESTler), and deployment. Built responsive web frontend with S3 static hosting and integrated ADA-compliant UI (WCAG 2.1 AA).
Impact & Results
- ▸8 REST endpoints with complete package lifecycle management (upload, download, search, update, reset)
- ▸Automated quality scoring across 7 metrics: ramp-up time, responsiveness, correctness, bus factor, license compliance, dependency pinning, and code review fraction
- ▸Serverless architecture scaling within AWS free tier with minimal operational overhead
- ▸Presigned-URL security for time-limited (10-minute) S3 access, avoiding Lambda 6MB payload limits
- ▸Packages below 0.5 average score automatically rejected during ingestion
- ▸Comprehensive STRIDE threat model analysis with IAM policies and CloudWatch audit trails
- ▸CI/CD pipeline with Jest unit testing (80%+ coverage), TypeScript linting, and RESTler security testing